
Understanding the Security of Bubble: Building Secure Applications in a NoCode Environment
.png)
Understanding the Security of Bubble: Building Secure Applications in a NoCode Environment
Published on February 8, 2025
By Christiam Muñoz . 10 minute read
As the demand for NoCode and LowCode development platforms continues to rise, many businesses and developers are exploring tools like Bubble.io to create applications without extensive coding knowledge. However, security remains a paramount concern, especially when targeting corporate clients.
The Security Framework of Bubble

Bubble.io is designed with a comprehensive security framework that adheres to industry standards.
1. Data Protection Measures
- Encryption: All data transmitted is encrypted using HTTPS (TLS). Data at rest is secured with AES-256 encryption.
- User Authentication: Bubble's built-in authentication supports two-factor authentication (2FA) and single sign-on (SSO).
- Privacy Controls: Users can define granular privacy settings to control access to different data items.
Compliance and Design Best Practices
Bubble.io adheres to SOC 2 Type II and GDPR regulations, and undergoes regular penetration testing to identify vulnerabilities.
Best Practices for Building Secure Applications with Bubble
Implement Strong User Authentication
Developers should enforce password complexity requirements, enable 2FA, and consider implementing SSO for corporate clients.
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities within the application. Developers should review logs for unusual activity and perform routine checks on privacy settings.
Role-Based Access Control (RBAC)
Implementing RBAC allows developers to assign specific permissions based on user roles, ensuring users have access only to information necessary for their tasks.
Advanced Security Features in Bubble
- DDoS Protection: Through its partnership with Cloudflare, Bubble provides built-in DDoS protection.
- Point-in-Time Data Recovery: Allows users to restore historical versions of their data.
- Extensive Logging: Bubble maintains detailed logs of application activities.
Conclusion
Bubble.io provides a robust platform for developing secure applications without extensive coding knowledge. By leveraging its built-in security features and adhering to best practices, developers can create applications that meet corporate security standards.
Related Articles

Zero Data Retention (ZDR): Does Your Business Actually Need It to Use AI in 2026?
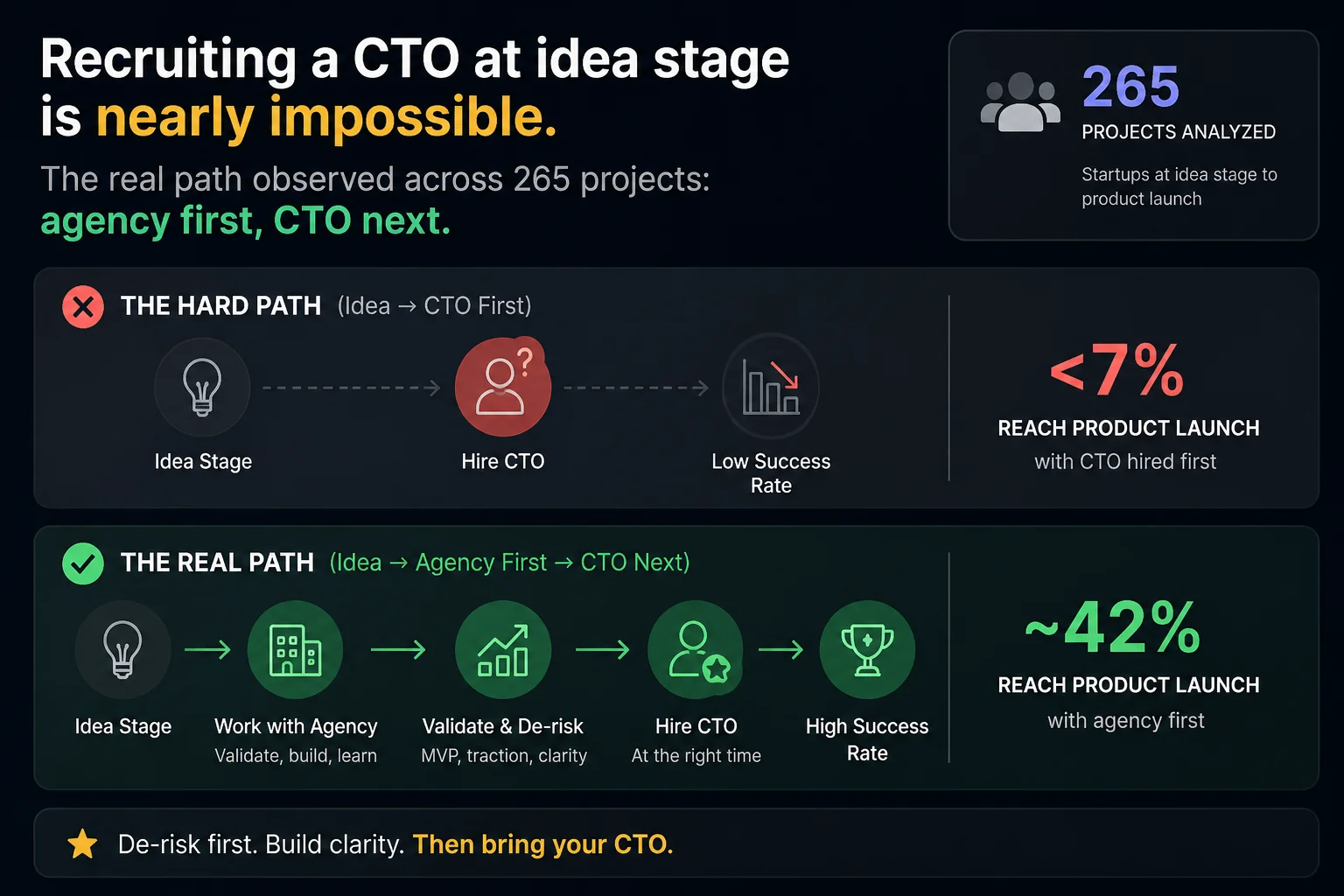
Co-founder CTO or Agency Partner: The Real Path of an Early-Stage Tech Founder



.png)


.svg)
